The accelerated adoption of mobile devices such as tablets and smartphones in the consumer world now is a catalyst for change in the manufacturing industry. According to Manufacturing Executive, 63% of manufacturing companies permit their employees to bring their own devices to work.
While manufacturers recognize the benefits to providing employees with flexibility to access manufacturing and business systems locally or remotely over employee-owned devices, only 17% of manufacturing enterprises have a formal bring-your-own-device (BYOD) strategy with clear goals and objectives.
Whether enabling work to be done on an employee’s personal device, enabling the sharing of plant-floor and enterprise applications with external partners, enhancing the availability of corporate learning and safety and security resources, or empowering subject matter experts (SMEs) to service equipment and review designs wherever they may be physically located, employees and senior management want this kind of flexibility.
Benefits to BYOD
BYOD programs aren’t just about satisfying employees. They’re about how effectively they drive efficiency and help your manufacturing business achieve its fundamental objectives, such as:
Supply Chain Agility. BYOD strategies can help you connect in real time to supply warehouses, production facilities, and the field (including distribution channels). You also can integrate this data with enterprise resource planning (ERP), manufacturing execution systems (MES) and customer relationship management (CRM) applications.
Continuous Innovation. The ability to integrate different types of communications such as voice, video and data on different mobile devices and software platforms increases the efficacy of communicating across functions, levels of expertise and even language barriers.
Operational Excellence. BYOD solutions allow manufacturers to monitor and control day-to-day functions of multiple business lines and facilities in rich detail. Best practices can be captured and shared across operations, and processes can be tuned or enhanced based on information made available anywhere, anytime, on any device throughout the entire value chain. SMEs can be quickly identified to address complex issues, and approvals and decisions can be accelerated with paperless workflows.
An important challenge is to deliver a secure, high-quality user experience across multiple platforms and devices (including Apple iOS, Android and Windows).
To deliver these experiences, IT organizations must design, deploy and maintain an architecture that:
- Secures both corporate and noncorporate devices, and enforces policy to protect intellectual property.
- Scales infrastructure to meet the growing number of devices per user.
- Increases productivity through quality of the user experience.
- Integrates real-time manufacturing enterprise applications, including SCADA, MRP and MES, with plant-floor instrumentation and production data in real time.
- Delivers rich voice and video data for increased workflow collaboration and productivity anywhere and on any device.
- Simplifies management and provisioning of software, lowering operational costs.
Armed with the right tools, manufacturers can cost-effectively use BYOD strategies to innovate, optimize and drive productivity without compromising the way their business works.
Alleviate the Risks
For any widespread adoption of BYOD, a number of considerations need to be considered beforehand.
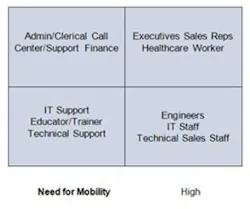
Understand user segments and needs. It’s important to understand that there are different segments of users within any BYOD implementation. One recommendation is to conduct a user segmentation analysis within the company to help understand the needs and likely level of required support (see Figure 1).
For example, BYOD deployments are easy with users who only need low levels of IT support, possibly using self-support communities to share best practices. Deployments might be more difficult with users who have high mobility needs but also require high support levels, such as executives.
Conducting such an analysis will help understand entitlement policies and support models and might prevent frustration and cost overruns in the IT budget.
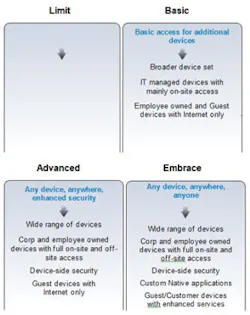
Decide on a BYOD adoption strategy. Different businesses will approach BYOD with different expectations across a spectrum of adoption scenarios. Every business needs a BYOD strategy, even if the intention is to deny all devices except IT-approved and IT-managed devices.
Figure 2 shows a number of possible adoption scenarios into which most businesses fit.
For many companies, adoption will range from allowing a broad set of devices with restrictive access to applications to embracing BYOD in full, encouraging adoption of many or all device types and deploying security measures to enable access to numerous enterprise applications and data.
Some companies will adopt a “mobile first” strategy, where their own internal applications development will be prioritized on tablets and smartphones, seeking competitive advantage by leveraging the broadest set of productivity tools and devices.
Understanding where your business will fit now and in the future along the BYOD adoption spectrum is useful to prepare for security policies, entitlement and overall strategy.
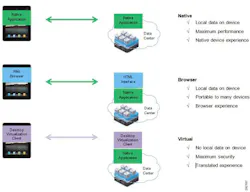
Understand native, browser and virtual modes. Securing and preventing the loss of corporate data is a top concern when implementing BYOD. It’s important to understand three possible application architectures and the trade-offs involved: native, browser and virtual (see Figure 3).
In native mode, applications running on the device communicate directly with the application server in the host data center (or cloud). Data may be exchanged and stored directly on the BYOD device. Typically, the application performance and user experience are closest to the specific device; in other words, a business application functions much like any other application on the device. All the productivity benefits and device behavior are preserved and applications can be tailored to provide enhanced experiences.
A browser approach is increasingly being adopted for application access because of the ease of portability across devices and operating systems. Any device with a standard HTML browser capability can be used to access the application.
However, much like native mode, data can be exchanged and stored directly on the BYOD device, leading to security challenges and concerns about data loss. In addition, there might be some sacrifice of user experience.
To contrast, virtual mode applications exist on the application server in the data center or cloud and are represented through a VDI client on the device. Data is not stored locally on the mobile device. Only display information is exchanged and rendered on the BYOD device.
While this method provides maximum data security, user experience might be compromised because of the translation from an application server to the form-factor and OS native to the mobile device. Early adopters of this approach have provided somewhat negative feedback.
Online Community Demonstrates Power of Industrial IP:
A new source of network technology information, the Industrial IP Advantage community, offers guides, case studies, white papers and discussions on how standard Internet Protocol (IP) networking technologies can be used throughout the Connected Enterprise to boost productivity, efficiency and flexibility. Industrial IP Advantage promotes the idea that manufacturing and other industrial firms can build more successful businesses by deploying a secure, holistic, digital-communications fabric using standard, unmodified IP. Companies can turn this vision into reality through connectivity that drives better business intelligence, increased profitability and reduced costs. Industrial IP Advantage was established by Cisco, Panduit, Rockwell Automation and ODVA. They joined together to educate the market on the benefits of Ethernet, Internet Protocol and EtherNet/IP™. To learn more, visit www.industrial-ip.org.It’s important to decide which mode, native or virtual, will be used for the application architecture. Many companies might use a hybrid approach, using native mode for many standard business applications and virtual mode for a subset of applications with stricter confidentiality or sensitive data requirements.
Adopt an encompassing end-user agreement. Although not part of the network architecture, one area that must be well thought out prior to any BYOD implementation is the end user agreement (EUA). Because of the mixing of personal and corporate data, and the potential of having employee-owned devices being used for work, it’s critical to outline policies up front and be sure to communicate these to employees in advance.
IT organizations need to familiarize themselves with laws, including the Computer Fraud and Abuse Act, the Wiretap Act, and Communications Assistance for Law Enforcement Act (CALEA).
Read more on how properly deployed security technology, policies, procedures and behavior help manage risk.